When you’re using Azure WAF and Azure Active Directory OpenID Connect, you can experience the WAF blocking on the rule: SQL Comment Sequence Detected.
This is the real solution, please don’t use the solution that Microsoft Azure gives you, it’s very dangerous.
Microsoft Azure – Dangerous way
When you ask the support, they escalate and the only solution that they give you is: you need to disable this rule.
What The Hell!
They want us to disable the rule for the entire WAF so the entire traffic.
It’s easy to see that Microsoft will never change about stupid things and also about their services.
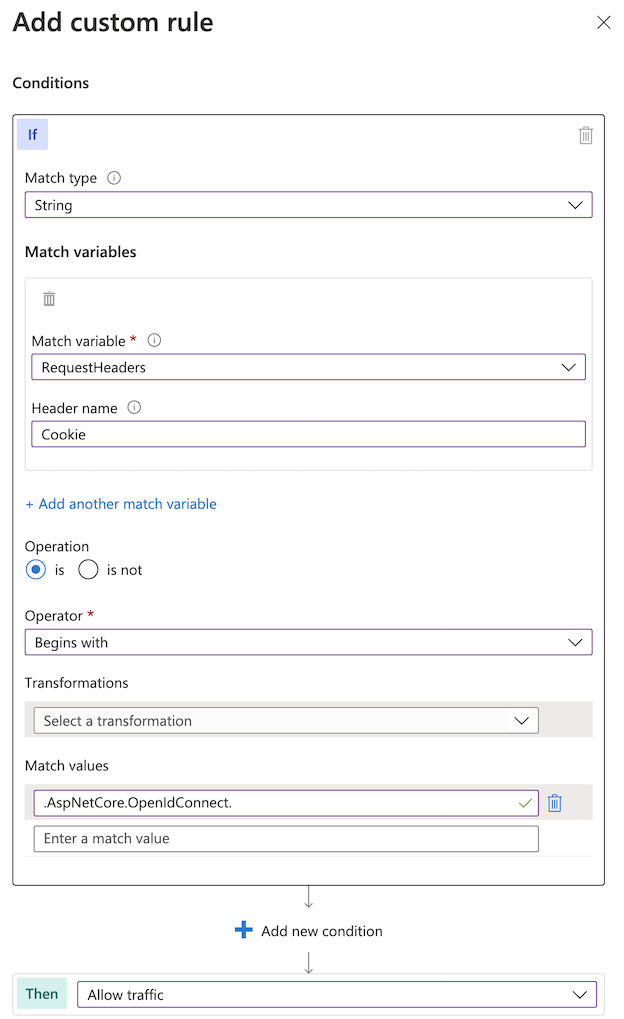
The Right Way: Custom Rule
We just need to allow the traffic on a specific setting: a value at the beginning of a cookie.
It’s not a joke, I use it in production and it works.
The logic:
If: String
Match:
- variable RequestHeaders
- Header name: Cookie
Operation: is
Operator: Begins with
Transformations: keep empty
Match value: .AspNetCore.OpenIdConnect.
Then: Allow traffic
Screenshot from Azure Portal
Never forget
When you need to write and enable custom rules, keep in mind to restrict to required URLs when it’s not affecting all endpoints.
